What do we offer?
In this competition, we offer free of charge the tailoring and testing of our end-to-end authentication and encryption solution of the satellite link on your specific architecture, in space and on the ground.
ARCA SATLINK product consists of a pair of cryptographic libraries: one to be deployed on the ground, while the other to be deployed on a satellite’s On-Board Computer (OBC) or communication subsystem.
ARCA SATLINK Space is a flight SDLS Library that aims to help satellite integrators facilitate and accelerate the implementation of a secure end-to-end communication link compliant with the CCSDS Space Data Link Security (SDLS) standard. The space library exposes all procedures described in the SDLS standard in order to secure frames and thus the datalink.
ARCA SATLINK Ground provides the same function described in the SDLS standard to secure downlink and uplink frames from and to the satellite end-point. It can be provided as a library or as a service, executed on premise or on the cloud.
These two ARCA STALINK components will ensure the basic functions of the CCSDS SDLS Protocol that is to say Apply Security and Process Security. These functions are the ones authenticating and encrypting your frames accordingly with the algorithm of your choice.
What is not included in this competition, even though it is already supported in our solution, is the extended procedures for keys and security associations management, over-the-air-rekeying (OTAR) as well as monitoring and controlling services.
The usage of ARCA SATLINK to secure TMTC and payload data brings forth a range of substantial benefits:
- End-to-end Security: ARCA SATLINK protects satellite communications end-to-end, preventing eavesdropping of critical data, mission control impersonation by a malicious operator, replay attacks, etc.
- Easy integration: ARCA SATLINK has been designed to be integrated and operated by clients with no or very little expertise in cybersecurity and cryptography. Its “dummy-proof” cryptographic service and library offers a user-friendly API which prevents any mistakes in the implementation of cryptographic operations.
- Compliance with customer requirements: Nowadays, satellite operators are more and more often required to comply with security requirements and/or national or international regulations, imposing some cyber protection of critical data like encryption and authentication of TMTC and payload data.
- Based on standards: ARCA SATLINK is a proprietary implementation of the CCSDS SDLS and SDLS-EP standards leveraging well-known cryptographic primitives.
Who shall apply?
This campaign is meant for every company or organization who intends to use satellite technology and services to improve their business. Within this campaign, ESA is promoting the use of satellite and security services and products to companies without the knowledge and infrastructure to do so. The intention is to boost commercialization of the mentioned services for innovative projects and ideas in line with ESAs Agenda 2025.
Companies and organizations that meet the technical requirements and want to use this product to improve their business are recommended to apply for this campaign.
Eligibility Criteria:
- The Applicant must be a juridical entity, registered in one of the ESA Member States, or one of the ESA Associate Members or Canada.
- The applicants must comply with the following key acceptance factors:
- Communication Protocol: The space-ground communication shall apply to the CCSDS standards
- Access to CCSDS Frames: Users should have access to CCSDS frames that they intend to protect using ARCA Satlink. This may involve receiving, transmitting, or processing CCSDS frames within their specific application or system.
- Processor: The SW Library can be deployed on several types of processors as long as the client can provide the compilation toolchain. Otherwise an ARM architecture is preferred.
- Memory: 1MB RAM to run the library and a Non-Volatile Memory (NVM) of up to 1 MB minimum required for file storage. (these are orders of magnitude)
- Permissions: Users should have appropriate permissions to install and run software on the target ARM-based system.
- Development Tools: Users may need development tools and libraries for building and linking applications with the cryptographic library. This includes a C compiler (e.g., GCC), make utility, and development headers.
What do you need to submit?
The submission if a form where you will have to concisely describe, through a list of precise questions :
- Your administrative details and your idea abstract for using ARCA SATLINK
- The technical details which will help us understand the scope of development needed to integrate both space and ground components on your architecture.
- The incentives that bring you to integrate security in your architecture and the role that security plays in your commercial perspective
- Your roadmap, which will help us vision your timeline to effectively deploy secured satellite links
Process
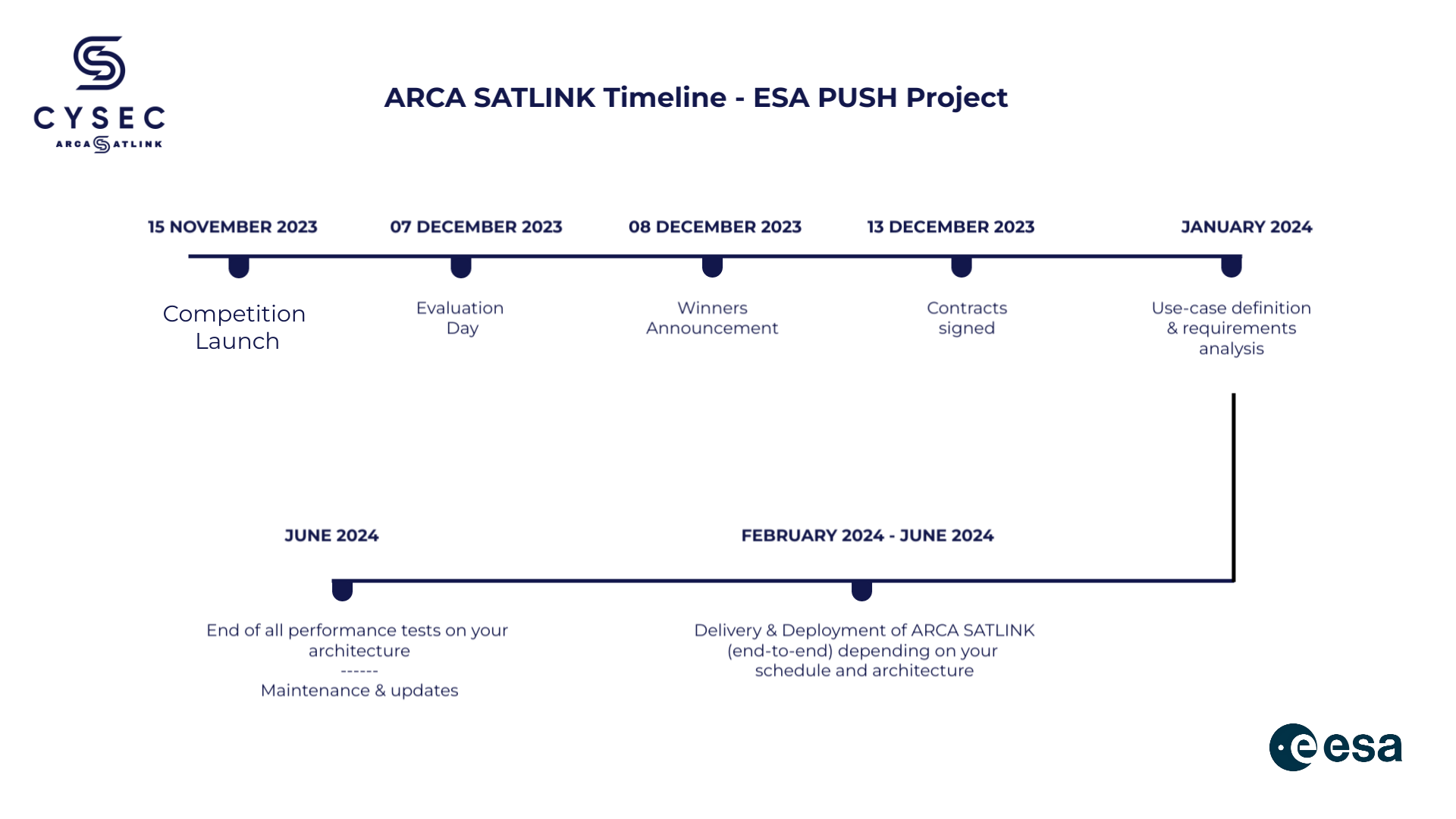
Step 1: Call for ideas: Launch of the competition happened on the 15th of November.
Step 2: Application & discussion phase: Companies and organization can apply by submitting their idea on OSIP until the 6th of December at midnight. Within this timeline there can be a discussion with the applying company/ organization to iterate the application and clarify open questions before the submission.
Phase 2: Eligibility assessment and evaluation phase: The highest ranked applicants in each theme will be selected and the contract shall be signed by the 13th of December.
Phase 3: Project executing phase: The project will start with a phase of alignment defining the use-case and analysing your specific requirements and architecture. Depending on your schedule and the effort needed to adjust to your architecture, the phase of deployment and delivery will happen between February and June 2024. In June the objective is to have finalised all the performance tests of ARCA SATLINK on your architecture. We will only have to do maintenance and updates if you decide to continue onwards with our solution.
All the different steps of the competition and project execution phase are summarised in the timeline below.