SECURING THE NEXT FRONTIER
Slide 2

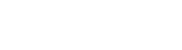
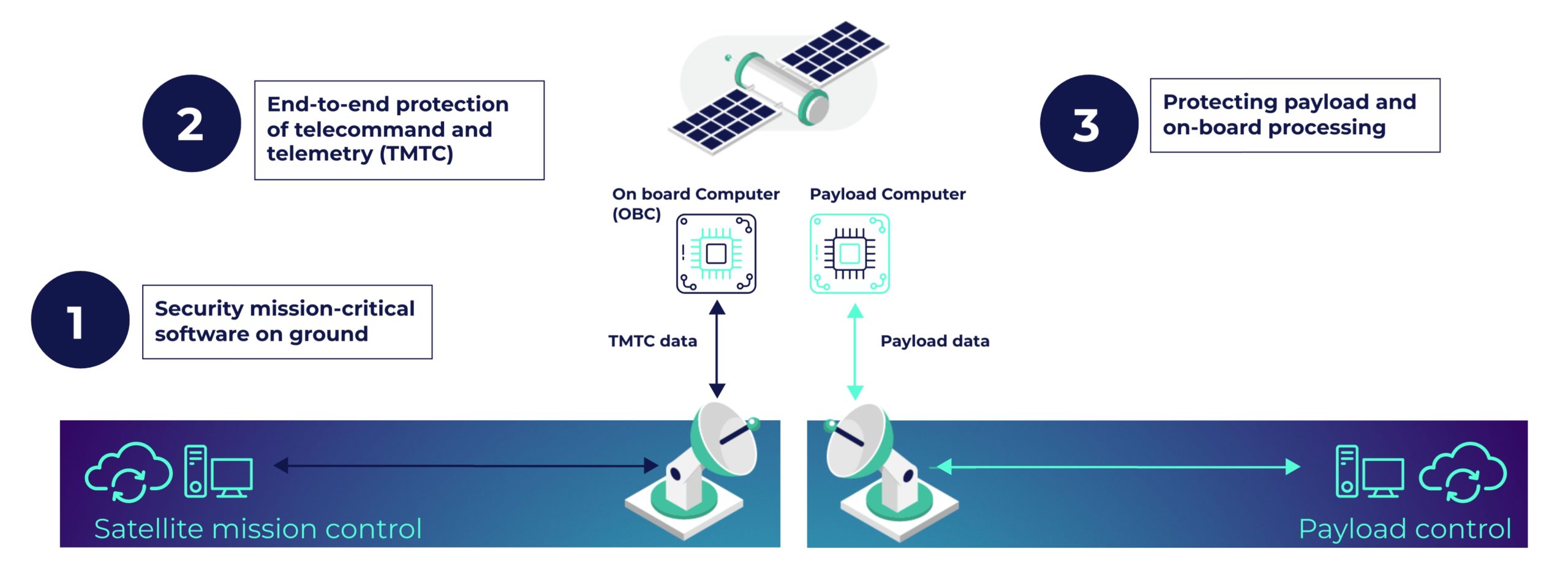
Designing the cybersecurity architecture of the Astrocast smallsat constellation
Slide 3
Designing the cybersecurity architecture of the ClearSpace ground segment
Slide 3

Deploying and testing a mission control software on a satellite simulator
Slide 3

Assessing the cybersecurity architecture of the Kleos smallsat constellation
Slide 3

Developing end-to-end security for satellite communications
Slide 3

In-orbit testing of cryptographic functions
Slide 3

Partnering for improving cybersecurity of Ground Segment as a service (GSaaS).