Containerization is a very effective approach to quickly deploy and manage workloads. However, the workload isolation provided by standard container runtimes is not as high as isolation from hardware virtualization technologies. Kata Containers, an independent open source community, is a secure container runtime based on lightweight virtual machines. It provides both the simplicity and speed of container management and the security isolation of virtual machines.
ARCA Trusted OS is a trusted execution environment based on a Kubernetes platform developed by CYSEC. This Kubernetes platform is composed of a hardened Linux OS, a Kubernetes orchestrator with secure settings and an API of cryptographic functions. The new release 1.5.0 of ARCA Trusted OS now embeds Kata Containers as an alternative OCI runtime to already existing standard runc and gVisor. Depending on its security policies, ARCA end-users can choose which runtime shall be used for the execution of each workload.
Kata Containers is an independent open-source community and detailed information on the project can be found here: https://katacontainers.io/
The benefits for the end-users are two-fold:
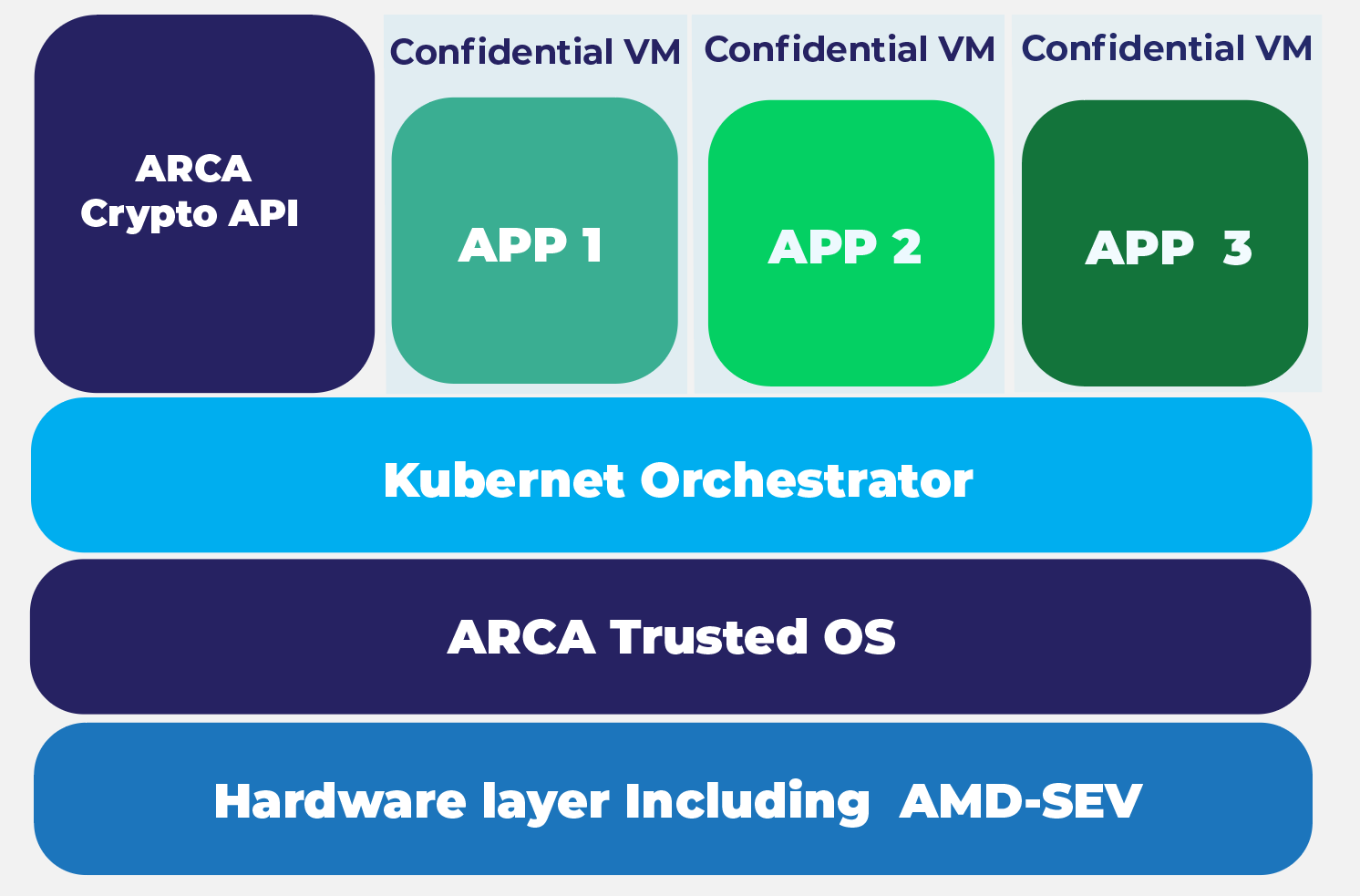
ARCA Trusted OS 1.5.0 can be executed in servers running with Intel or AMD CPUs. The selection of the Kata Containers runtime and the configuration of the TEE while running on AMD EPYC (e.g. with CYSEC appliances) can be performed in a very simple manner. These new features come in addition to the existing ARCA Trusted OS features, such as a hardware-based extended secure boot and other secure settings of ARCA Kubernetes platform.
The integration of Kata Containers is a major step in the CYSEC’s confidential computing product roadmap, complementing its previous secure Kubernetes offerings. With ARCA Trusted OS every part of the operating system is authenticated, and the integrity of the Kubernetes platform is verified, providing protection for your workloads while in-use.